phpcs-security-audit is a set of PHP_CodeSniffer rules that finds flaws or weaknesses related to security in PHP and its popular CMS or frameworks.
phpcs-security-audit is a set of PHP_CodeSniffer rules that finds flaws or weaknesses related to security in PHP and its popular CMS or frameworks.
It currently has core PHP rules as well as Drupal 7 specific rules. Next planned CMS/framework is Symfony 2, which are also relevant to Moodle.
As a bonus set of rules, the tool also check for CVE issues and security advisories related to CMS/framework. You can use it in order to follow the versioning of components during static code analysis.
The main reasons of this project for being an extension of PHP_CodeSniffer is to have easy integration into continuous integration systems and to be able to find security bugs that are not detected with object oriented analysis (like in RIPS or PHPMD).
phpcs-security-audit is backed by Floe design + technologies and written by Jonathan Marcil.
מקור: FloeDesignTechnologies/phpcs-security-audit
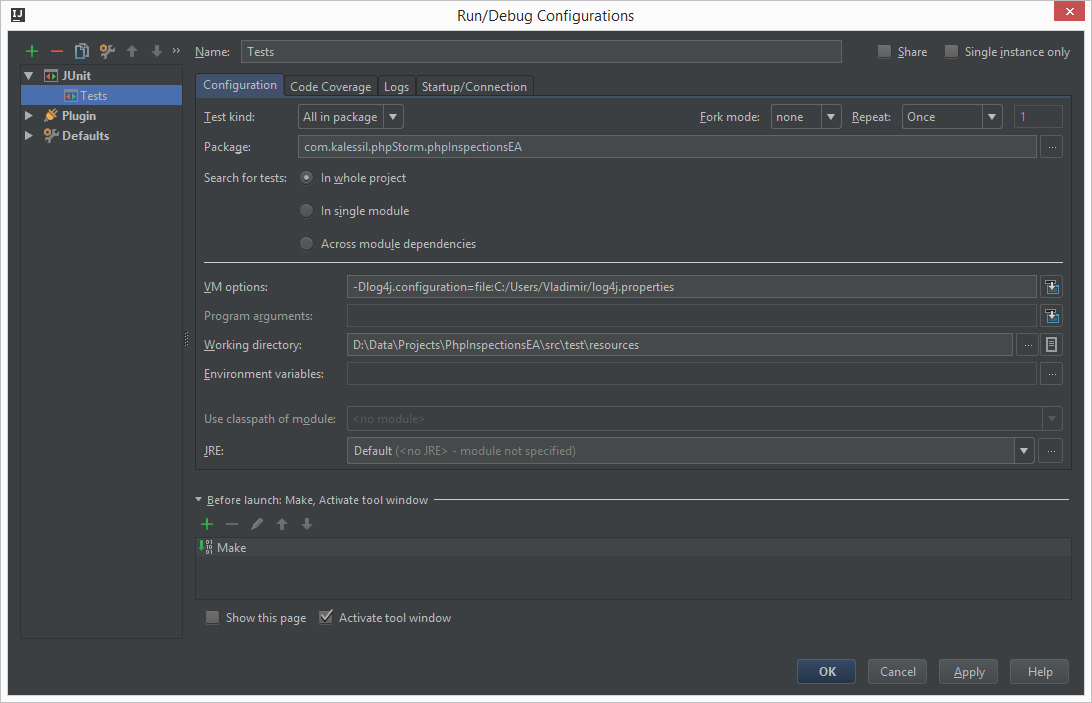
phpStorm setup
- Install: https://moodle.org/plugins/local_codechecker
- Git clone above github project (phpcs-security-audit)
- Follow project's README install instructions, and also…
- Copy https://github.com/FloeDesignTechnologies/phpcs-security-audit/tree/master/Security/Sniffs/BadFunctions folder into your Moodle local/codechecker/moodle/Sniffs
- Copy https://github.com/FloeDesignTechnologies/phpcs-security-audit/tree/master/Security/Sniffs/CVE folder into your Moodle local/codechecker/moodle/Sniffs